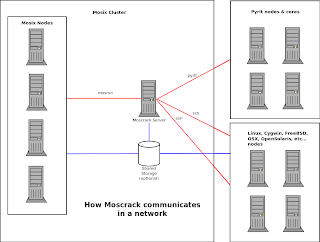
Moscrack is intended to facilitate the use of a WPA cracker on a cluster. Currently it has only been used with Mosix (clustering software) and SSH nodes. It works by reading a wordlist from STDIN or a file and breaking it into chunks and passing those chunks off to seperate processes that run in parallel. The parallel processes can then execute on different nodes in the cluster. All results are checked (to a degree) and recorded on the master node.
Version info
This release contains a new plugin framework that allows Moscrack to be extended beyond it's original design. Currently there are only two plugins. Pyrit and Dehasher. SVN will always have the latest bug fixes and enahancements. SVN download: https://moscrack.svn.sourceforge.net/svnroot/moscrackRequirements
Master server:
- Linux or possibly others- Mosix (optional)
- zenity (GUI support)
- Pyrit (optional)
- rsh/rcp clients (optional)
- scp client (optional)
- Perl 5.8
- Perl DateTime
- Perl Math::Round
- Perl Getopt::Lucid
- Perl Acme::Tools
- Perl Storable
- Perl Term::ANSIColor
- Perl File::Basename
- Perl Sruct::Compare
- Perl LWP::UserAgent
- Perl HTTP::Request
- Perl Net::SSH2
- Perl Compress::Zlib
- Perl Config::Std
End nodes:
Linux/Cygwin/FreeBSD/Solaris/MacOSX/iPhone all tested or Moscrack Live CD. One of Mosix, SSH v2 daemon, RSH daemon, Pyrit in serve mode. Aircrack-NG v1.1 unless using PyritInstallation
- Run ./install_modules to check for (and optionaly install) required Perl modules-Copy moscrack, mosctop, moscd to anywhere you like, possibly in your path like /usr/local/bin
- Copy moscrack.cgi to your web servers cgi-bin
- Edit moscrack.conf and copy to /etc/moscrack/moscrack.conf
- Copy plugins/ to /etc/moscrack/plugins/
- Create a working directory (home) for Moscrack (e.g. /opt/moscrack/)
- Edit nodes.dat and add all of your nodes and type. The format is documented in the file. Copy it to where you specified in the configuration file
- Tune nodes.dat (mandatory). See "Auto tuning mode" and optionaly "Performance" for details
- If using ssh nodes, setup public-key authentication with each node (e.g. ssh-copy-id user@node)
- If using rsh nodes, configure .rhosts file on each node
- Install Aircrack-NG on each node
- Make sure you can access all nodes (of any type) without a password
- Launch "moscd" if using dynamic nodes
- Run "moscrack"
- In another terminal, optionally run "mosctop" relative to the Moscrack working directory to watch what's going on .
DOWNLOAD : HERE



Post a Comment
I'm certainly not an expert, but I'll try my hardest to explain what I do know and research what I don't know. Be sure to check back again , after moderation i do make every effort to reply to your comments .